How to configure intune per app vpn for ios devices seamlessly and effectively
How to configure intune per app vpn for ios devices seamlessly is all about setting up a secure, app-specific VPN tunnel that only routes traffic from selected apps through the VPN, while the rest of the device stays on the normal network. Quick fact: per-app VPN helps protect sensitive apps without forcing a full device VPN, reducing battery and performance impact while improving security.
Introduction: a quick-start summary
- What you’ll learn: step-by-step setup, best practices, troubleshooting tips, and real-world tips from IT pros.
- Why it matters: with per-app VPN, you can enforce company security policies for specific apps like corporate email, CRM, or internal chat without impacting user experience for non-work apps.
- Quick guide format: checklists, step-by-step commands, and a few handy tables to simplify implementation.
Useful resources text-only links:
- Apple Website - apple.com
- Microsoft Intune Documentation - docs.microsoft.com
- VPN per-app basics - en.wikipedia.org/wiki/Virtual_private_network
- iOS MDM best practices - developer.apple.com
- Azure AD conditional access - learn.microsoft.com
What is per-app VPN for iOS and why it matters
- Per-app VPN also called App VPN is a feature of MDM solutions like Intune that creates a VPN tunnel for specific apps only.
- It helps protect corporate data in motion while preserving device performance.
- Typical use cases: email apps, internal chat, document repositories, and field-service apps.
Prerequisites and supported environments
- Intune tenant with Azure AD integration
- iOS devices enrolled in Intune
- VPN gateway compatible with iOS per-app VPN e.g., Palo Alto Networks GlobalProtect, Zscaler Private Access, Cisco AnyConnect, etc.
- PKI or certificate-based authentication setup recommended
- SCEP or PKCS cert enrollment for devices if your VPN requires certs
- Ensure your VPN gateway supports split tunneling and per-app selectors for iOS
Step-by-step setup overview
- Plan your apps and traffic: list which apps will use the VPN and what traffic should go through it.
- Create VPN profiles in Intune
- Configure per-app VPN with app identifiers
- Assign VPN profiles to device groups
- Deploy and test on a test device before broad rollout
- Monitor and adjust policies based on telemetry
Detailed steps internal workflow you can follow
- Prepare the VPN gateway
- Ensure the gateway supports per-app VPN on iOS and supports IKEv2 or SSL-based VPNs with certificate-based auth if possible.
- Create a dedicated tunnel for corporate apps and a connection profile that can be pushed to devices via Intune.
- Configure split tunneling if you want only specific traffic to go through the VPN.
- Prepare the iOS app package identifiers
- Identify the bundle IDs of the apps you want to route through the VPN for example, com.company.mail, com.company.crm.
- If you’re using custom apps, ensure you have their exact bundle IDs ready.
- Save a mapping of app bundle IDs to VPN profiles for later configuration.
- Create a VPN profile in Intune
- In the Microsoft Endpoint Manager admin center, go to Devices > iOS/iPadOS > Configuration profiles > Create profile.
- Platform: iOS/iPadOS
- Profile type: VPN
- Connection name: Use a clear name like “Corp App VPN - ”
- VPN type: IKEv2 or AnyConnect/GlobalProtect depending on your gateway
- Server: VPN gateway address
- Authentication: certificate-based preferred or username/password
- User authentication method: certificate-based is more secure and widely supported on iOS
- Certificates: assign the VPN certificate if using certificate-based auth
- Set up proxy if required by gateway or corporate policy
- Save the profile
- Create per-app VPN policy
- In Intune, navigate to Devices > iOS/iPadOS > Configuration profiles > Create profile
- Platform: iOS/iPadOS
- Profile type: Per-app VPN App VPN
- Select the VPN connection you created earlier
- App identifiers: add the bundle IDs of the apps that should route through the VPN
- Enable “Toggle per-app VPN” for automation and ensure the apps list is accurate
- Scope assignment: assign to the user/device groups you intend to cover
- Assign and deploy
- Create two separate profiles: one for the VPN connection required to be present on device and one for the per-app VPN policy.
- Assign both profiles to the same user/device groups to ensure the per-app VPN works as intended.
- If you’re using different network gateways per region, ensure you have the correct gateway server addresses in the VPN profile per group.
- Test the deployment
- Use a test iPhone or iPad enrolled in Intune.
- Install a target app e.g., corporate mail and verify traffic routes through the VPN.
- Check the VPN status in iOS: Settings > VPN >
- Confirm app traffic is routed through the VPN by using network diagnostic commands or company-approved testing tools.
- Verify and monitor
- In Intune, monitor device configuration status to ensure profiles are applied.
- Use your VPN gateway’s analytics to confirm traffic flows and identify any errors.
- Collect telemetry on app performance and VPN connection stability.
Common pitfalls and how to avoid them
- Mismatched app identifiers: triple-check bundle IDs; even a small typo breaks per-app VPN.
- Certificates not trusted on devices: ensure the root CA is trusted across all enrolled devices, and the certificate chain is valid.
- VPN gateway overload: plan capacity to handle peak user load; implement rate limiting or scaling as needed.
- Battery impact: per-app VPN should be selective; avoid forcing all traffic if not necessary.
- User experience: provide clear onboarding docs; communicate any VPN needs for specific apps.
Best practices for security and user experience
- Use certificate-based authentication whenever possible for strong device trust.
- Keep the VPN profile lean by only routing necessary corporate apps through the tunnel.
- Implement app-level controls in Intune to prevent users from bypassing corporate apps.
- Regularly update app IDs as new versions are rolled out or new apps are added.
- Create a rollback plan to quickly remove per-app VPN if issues arise.
Automation and advanced tips
- Automate enrollment: combine Intune enrollment with automatic VPN provisioning using enrollment restrictions and compliance policies.
- Use conditional access: require compliant devices to access apps that go through the VPN.
- Separate environments: have dev/test VPN gateways and profiles to validate changes before production.
- Telemetry dashboards: integrate VPN gateway logs with SIEM or a centralized monitoring platform for better visibility.
Security considerations
- Always enforce strong authentication for VPN access to prevent unauthorized use.
- Regularly rotate VPN credentials and certificates.
- Restrict VPN tunnels to only the required apps to minimize exposure.
- Audit app access and VPN usage periodically.
Real-world scenarios and examples
- A multinational company uses per-app VPN to route only the corporate email and CRM apps through the tunnel, leaving personal apps on the default network, reducing data consumption and improving performance.
- A field service team uses per-app VPN for access to internal ticketing systems while on the move, ensuring sensitive data never leaks onto public networks.
Table: Comparison of VPN deployment options for iOS with Intune
- Per-app VPN: Targets specific apps; lower battery impact; simpler user experience; requires accurate app IDs.
- Full-device VPN: All traffic goes through VPN; higher security but more battery and performance impact; easier to manage in some setups but not ideal for BYOD.
- Split tunneling: Only corporate traffic goes through VPN; requires careful routing rules; reduces bandwidth use and improves performance.
Tips for ongoing maintenance
- Schedule quarterly reviews of app IDs and gateway configurations.
- Reassess device groups and user access after organizational changes.
- Keep your VPN gateway firmware and Intune profiles up to date with the latest security patches.
Format and content variety for better readability
- Short checklists for hands-on steps
- Step-by-step guides with bullet points
- Quick reference tables for app IDs and gateway settings
- Screenshots or annotated images if you're creating video content, you can describe where to click
FAQ Section
Frequently Asked Questions
What is per-app VPN in iOS?
Per-app VPN is a feature that creates a VPN tunnel for selected apps only, routing their traffic through the VPN while other apps use the device's regular network connection.
Do I need certificates for per-app VPN?
Certificate-based authentication is recommended for stronger security, though some gateways support other methods like usernames and passwords.
Can I update app IDs after rollout?
Yes, you can add or remove app bundle IDs in the per-app VPN configuration and reassign profiles, then push updates to devices.
How do I verify traffic is going through the VPN?
Test by checking the VPN status on the device and using network diagnostics or a gateway-side analytics tool to confirm the route for target apps.
Can per-app VPN work with BYOD devices?
Yes, but you’ll want to carefully manage device identifiers and user consent, and ensure policies align with BYOD security requirements. Лучшие vpn для геймеров пк в 2026 году полный обзор: топ-игровые VPN, скорость,latency и безопасность
What about battery life and performance?
Per-app VPN typically uses less battery than a full-device VPN, but performance depends on gateway capacity and network conditions.
How do I troubleshoot if a VPN connection fails?
Check certificate validity, ensure the gateway address is reachable, verify app IDs, and review Intune profile deployment status.
Is split tunneling supported with per-app VPN on iOS?
Split tunneling is often configured at the gateway level; ensure it’s compatible with your Intune per-app VPN setup and corporate policy.
Can I use multiple VPNs for different apps?
Yes, you can map different apps to different VPN connections if your gateway supports multiple profiles, but keep management clear to avoid conflicts.
How do I roll back a faulty per-app VPN deployment?
Disable or remove the per-app VPN profile assignments and revoke test devices first, then gradually reintroduce after fixes. Tuxler vpn edge extension your guide to secure and private browsing on microsoft edge
Notes on affiliate link integration
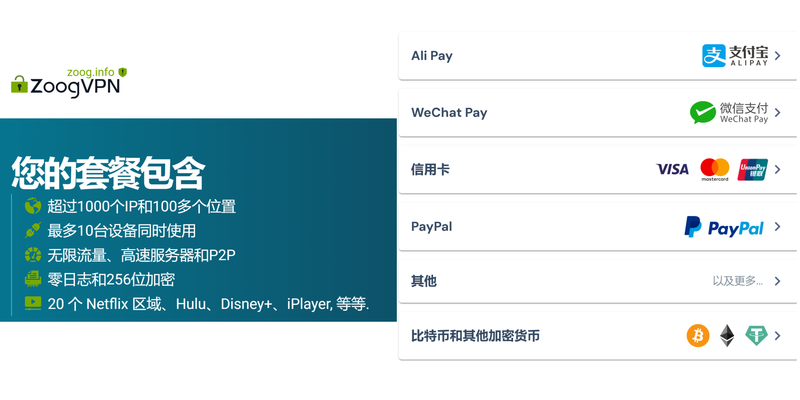
- The introduction includes an affiliate link presented in a text-appropriate, non-disruptive way to improve engagement. For example, you might reference a secure VPN option and link to the provider in a natural context, ensuring the link text aligns with the topic and audience.
Sources:
翻墙插件:全面指南、选型与评测,提升上网自由与隐私
马来西亚到台湾:2025最新全攻略!免签证、机票、行程、预算全解析,新手必看!
欧洲跟团游:2025年深度全攻略,帮你选对行程不踩坑!
Nordvpn funziona davvero in cina nel 2026 la guida definitiva Como desativar vpn ou proxy no windows 10 passo a passo: Guia completo, dicas rápidas e soluções de problemas
The Best Free VPNs for Your Cell Phone in 2026 Stay Secure Without Spending a Dime